Projects
Here are some projects that I have done:
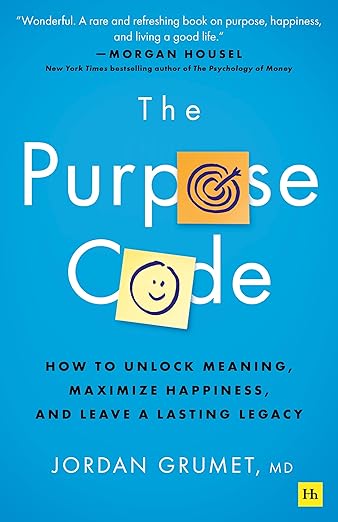
MemQuotes - Movie Quote Tracker
November 2025 - Present
This application is:
- Full-stack web application for cataloging memorable quotes from movies, TV shows, and books
- Built with React, Custom CSS animations, and Lucide Icons
- Deployed on Vercel with GitHub CI/CD integration
- Advanced filtering system with timestamp-based search and multi-genre tagging
- Interactive features: collapsible cards, audio uploads, and animated cinematic UI
- Built with assistance from Claude AI
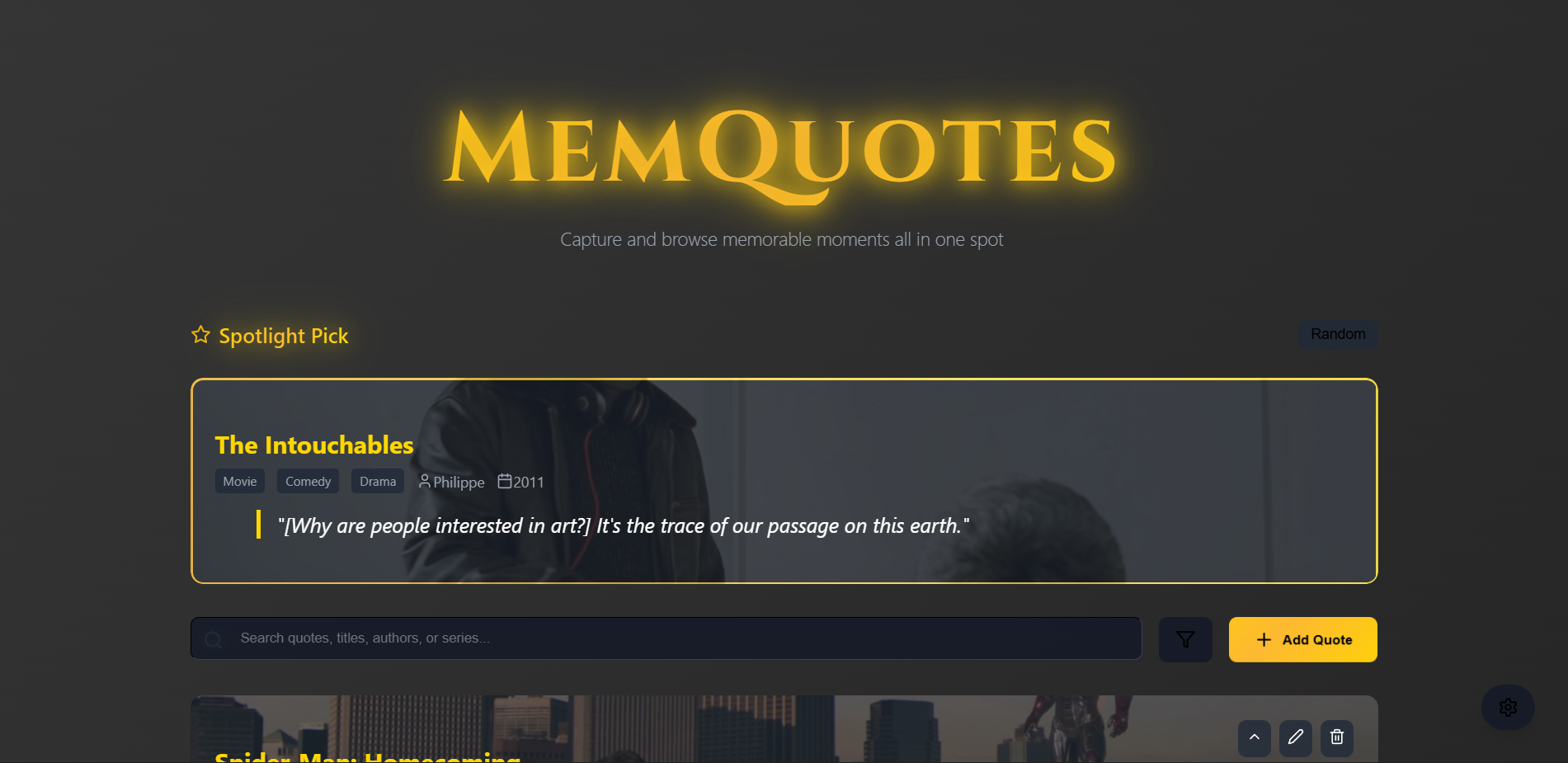
Personal Portfolio Website
June 2025 - Present
This project features:
- Built using AI collaboration – Leveraged DeepSeek for initial code structure, then customized with personal content, styling, and images
- Modern, responsive portfolio – Features dark/light mode toggle, typewriter effect, and organized project showcase with date ranges
- Showcases cybersecurity & development skills – Highlights technical projects, tools, and academic experience in a professional layout
- Deployed via GitHub + Vercel – Fully hosted portfolio with clean UI, embedded resume, and social links for recruiters and connections
Enterprise WAN Network Design & Implementation
June 2025 - September 2025

In this project I used Boson's NetSim tool to:
- Designed and built a secure WAN connecting a corporate headquarters to a remote office using Cisco routers, implementing PPP with CHAP authentication
- Architected the local network at the remote office using Layer 2 switches, configuring an EtherChannel trunk for high availability and increased bandwidth
- Automated client configuration by deploying and managing DHCP services on both site routers for seamless device onboarding
- Enabled full network communication between sites by implementing and verifying the RIPv2 dynamic routing protocol
- Validated end-to-end functionality through rigorous testing, successfully achieving connectivity from a remote PC to a headquarters PC
- Created comprehensive technical documentation, including a network diagram, configuration specs, and verification steps
Nostromo Linux Penetration Testing
June 2025 - September 2025

In this project I gained root access via privilege escalation by:
- Executed a full penetration testing lifecycle: from initial reconnaissance and enumeration to exploitation, privilege escalation, and proof capture
- Discovered and exploited a critical Remote Code Execution (RCE) vulnerability (CVE-2019-16278) in the Nostromo 1.9.6 web server to gain an initial foothold on the system
- Leveraged misconfigured service permissions to access sensitive data via anonymous FTP login, uncovering a note that revealed the location of password hashes
- Cracked a user password hash using hashcat and .txt wordlist, demonstrating the risk of weak password policies and outdated hashing algorithms (MD5)
- Performed privilege escalation by exploiting sudo misconfigurations
- Documented the entire process in a professional penetration test report, including detailed findings, proof-of-concept commands, and critical mitigation strategies
Android Application Reverse Engineering
March 2025 - June 2025

In this project I hacked into a andriod application by:
- Imported IntroAndroidSecurity virtual machine and manually install Andriodx86 virtual machines on Oracle VirtualBox
- Installed Andriod CrackMe One and CrackMe Two applications through .apk files in jadx-gui
- Navigated through CrackMe Two application's source code and identified hash method used to store password in application
- Unhashed password stored in application source code to get passsword in plaintext
- Gained access to application using username and unhashed passsword
Industrial Control Systems (ICS) Vulnerability Analysis
June 2024 - September 2024

In this project I collaborated with team members to:
- Aggregated and compiled international ICS data from universities worldwide
- Preprocessed raw ICS data for analysis utilizing Python, Bash, and Excel
- Engineered complex Oracle SQL queries to transform raw data into structured, meaningful datasets for analysis
- Visualized complex security vulnerability data in Tableau and PowerPoint to guide risk-based decisions
Steam Games Dataset Analysis
June 2024 - September 2024

The focus of this group project was to analyze data about steam games through:
- Cleaned and processed raw steam games data from Kaggle using Python and Oracle SQL
- Designed and implemented a normalized relational database through Vertabelo and Oracle SQL Developer
- Leveraged advanced Oracle SQL queries to uncover key trends in pricing, genres, and user ratings
Nature Exploration App Design
April 2024 - June 2024

In this project I collaborated with three team members to:
- Brainstormed and explored technical nature exploration ideas using the Double Diamond Method
- Designed an nature exploration app using Canva and Figma
- Tested app designed via questionnaires and Lyssna
- Filtered and sort feedback to incorporate user assessment into app deisgn
Drexel Penetration Testing
April 2024 - June 2024

Took on the role as a Project Manager in a team setting to:
- Participated in Drexel University Information Technology's Bug Bounty Progam
- Directed the full project lifecycle for a penetration testing initiative, facilitated weekly meeting for progress review, strategic planning, and task delegation
- Scanned internet accessible resources within the drexel.edu domain using penetration testing tools
- Performed penetration tests against multiple targets identified through sorted scan results
- Authored comprehensive vulnerability and mitigation reports for Drexel IT; credited for the discovery of a critical security vulnerability
Times Entertainment
September 2023 - December 2023
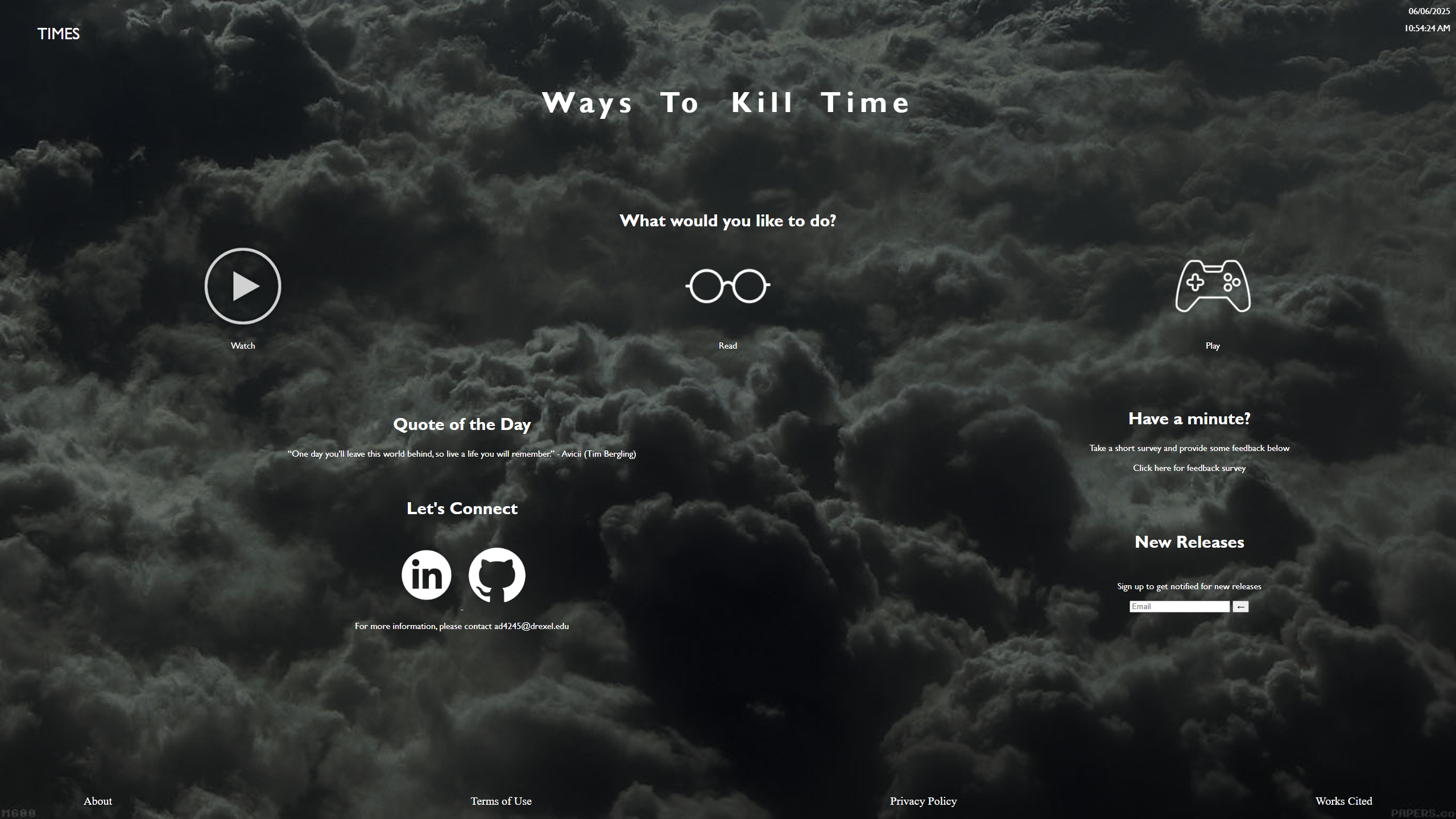
This website offers a small collection of things to do in one's spare time
- Displayed content to watch, read, and play using HTML and CSS
- Used JavaScript to: display date and time, randomly select and display quotes, and allow family safe filter for website content
- Accomplished website content filtering and display with combination of HTML and JavaScript
Pendragon Mount
September 2023 - December 2023
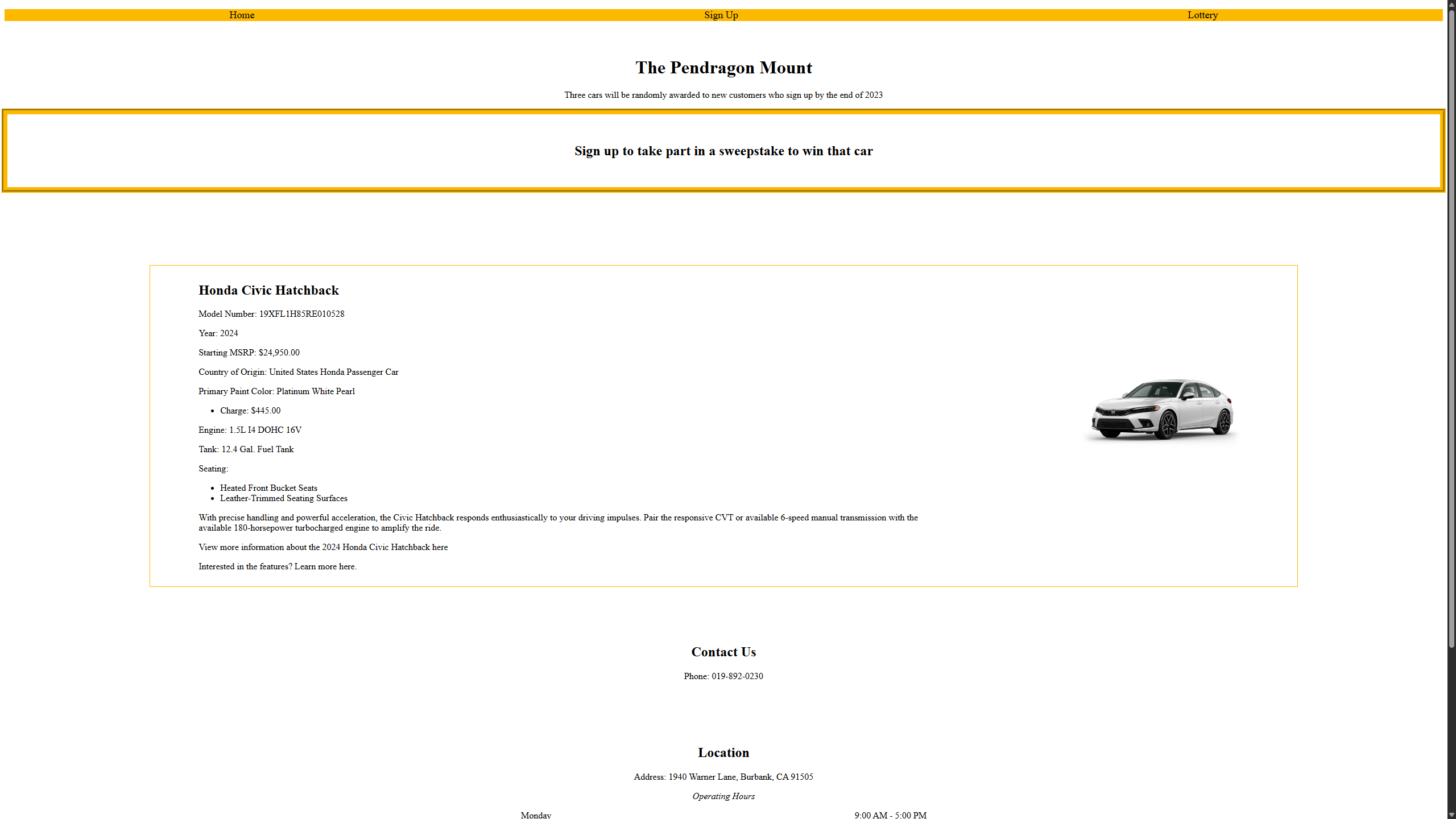
This website is designed to mimic a typical sweepstakes process
- Designed website with HTML and CSS to display information about the sweepstake rewards, form fields, and various lottery information
- Utilized JavaScript for logic behind data manipulation, survey form fields refresh, and webpage appearance
- Implemented buttons to preform survey processes